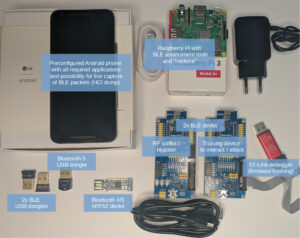
Each attendee will receive a hardware pack of 200 USD value, shipped in advance (please register as soon as possible!). The hardware includes among others a preconfigured Android smartphone, BLE sniffer, BLE dedicated training device and Raspberry Pi (details below). With the specially arranged setup, participants will be able to perform hands-on practical exercises not only during virtual session but also any time later.
$2,499.00
| Date | Day | Time | Duration |
| 24 August | Tuesday | 09:00-17:00 SGT/GMT +8 | 8 Hours |
| 25 August | Wednesday | 09:00-17:00 SGT/GMT +8 | 8 Hours |
Bluetooth Low Energy is one of the most commonly used and rapidly growing IoT technologies. We are immersed in surrounding BLE signals: starting with COVID-19 contact tracing apps, through beacons, wearables, TVs, home appliances, toothbrushes, sex toys up to smart locks, medical devices and banking tokens. Unfortunately the prevalence of technology does not come with its security, resulting in alarming vulnerabilities revealed day by day. And yet, the knowledge on how to comprehensively assess security of such devices still remains rather uncommon.
This is probably the most exhaustive and up to date training regarding BLE security. Multiple hands-on exercises cover BLE sniffing, MITM, relay, jamming, hijacking, cracking, proprietary protocols, logic vulnerabilities in many real devices (dozen smart locks, U2F or banking authentication tokens, mobile PoS). And what’s best: all the hardware required is included and shipped to you in advance! Most exercises will be performed on specially developed, included training BLE device to attack, but you will also have possibility to remotely hack real ones (like smart locks) – using BLE relay proxy via Internet. You will finish the training being able not only to fully assess and compromise BLE devices, but also with the equipment to do it.
1. What is Bluetooth Low Energy – introduction. 2. BLE advertisements - broadcasted packets a) Theory - BLE advertisement packets b) Scanning for nearby BLE devices’ advertisements using various tools: mobile applications, BlueZ command-line, other tools (bettercap, Mirage, GATTacker, …) c) BLE Beacons - iBeacon, Eddystone, - Spoofing/cloning beacons to get rewards, free beer, or activate connected underwear - Tracking devices (key finders, …), crowdsourced location d) Apple, Microsoft devices BLE advertisements - Find out nearby Apple devices and their state by their BLE broadcast packets - How to recover phone number and Apple ID from iPhone BLE advertisements - Is it possible to track specific Microsoft device using its BLE broadcasted signal? - Apple Airtag ("Find My") e) COVID-19 contact tracing / exposure notification BLE packets f) Other BLE advertisements - energy meters revealing current indication, sex toys revealing device model, … g) Bleedingbit - RCE chain via improper BLE advertisements parsing Skills: understand BLE advertisement packets, ability to identify and spoof BLE devices, knowledge of using various BLE tools. 3. BLE connections a) Theory introduction: GATT specification, central vs peripheral device, services, characteristics, connections, … b) Connecting to your dedicated BLE device using various tools - nRF Connect mobile application: read/write/notify, automation with macros. - BlueZ command-line: gatttool - other tools: Bettercap, GATTacker, … c) Taking control of simple insecure devices (BLE dildo, key finder, ...) Skills: understand BLE connections, ability to exchange data with devices using various tools, taking control over the simplest devices that do not implement any security. 4. Sniffing BLE a) BLE RF layer theory introduction - Radio modulation, channels, hopping, connection initiation - Why so many devices do not encrypt link-layer - Various sniffing hardware and software options b) Sniffing live raw BLE packets from the air using provided hardware and Wireshark - Wireshark tips&tricks - Capture your own connection from mobile app to your BLE device - How to combine multiple sniffers for better reliability c) Sniffing demos: smart lock plain text password, banking token OTP d) Other hardware and open source sniffers: Ubertooth, Btlejack, Sniffle, SDR, … Skills: understand BLE radio layer, ability to use sniffing software and hardware, capture and analyse BLE packets in Wireshark. 5. BLE HCI dump – reliably capture own packets a) Difference from RF layer sniffing b) Android: connect provided, preconfigured smartphone directly to Wireshark via adb TCP service for live capture of your BLE packets c) Linux command-line hcidump 6. BLE “Man in the Middle” / remote relay d) Conditions for MITM, attack scenarios, MAC address cloning e) BLE MITM – remote relay your BLE connection via WiFi and provided Raspberry Pi f) Intercept and relay via Internet BLE communication of remotely located devices: sample smart lock and BLE dildo g) Abusing proximity autounlock feature via remote relay h) Tampering BLE packets via MITM - demo using mobile Point of Sale to alter information displayed on terminal. i) Various BLE MITM tools: GATTacker, BtleJuice, Mirage Skills: understand conditions for BLE MITM, remote relay, replay. Perform the attacks in practice.
7. BLE insecurity case studies a) Sample smart lock attack: decompile Android application, reverse-engineer BLE protocol commands, identify weakness in protocol, exploit in practice using mobile application b) Various attacks on proprietary authentication/encryption protocols based on real devices (including several smart locks). c) Abusing excessive BLE services, hardcoded credentials, remote access share functionality, cloud interface, ... 8. BLE link-layer security a) BLE link layer security mechanisms - introduction, levels, pairing, bonding, why most devices do not implement it at all. b) Pair the provided smartphone with your dedicated BLE device, sniff the pairing process and crack it with CrackLE. c) Attacks possible on paired/bonded connections d) BLE MAC address randomization, “silent pairing” attacks recovering Identity Resolving Key (for example leveraging contact tracing apps). e) Abusing trust relationships of bonded devices - vulnerabilities in HID devices, Google Titan U2F token vulnerability technical analysis, attacks via other applications installed on the same mobile phone, ... Skills: understand BLE link layer security and pairing/bonding. Ability to sniff, debug, crack the encrypted connection. 9. Provided BLE development boards a) Technical details about provided BLE devboards (nrf51, nRF52) b) How to develop own firmware (or alter the training device) using free online service or standalone tools. c) Review of provided firmware images / source (nRF sniffer, Btlejack, dedicated BLE device to attack) d) Flashing firmware via provided ST-Link debugger (nRF51) or USB (nRF52) Skills: Ability to flash various firmware images to provided devboards (sniffer, “smartockpicking” training device, btlejack, DFU target, …); alter/compile provided sources. 10. BLE jamming, injecting, hijacking a) Theory introduction: injecting via InjectaBLE attack, hijack BLE ongoing connections using BtleJack approach b) InjectaBLE attack in practice using Mirage and included nRF52 dongle c) Btlejack in practice - Flash btlejack firmware to your devices - Btlejack as BLE sniffer - Jam/intercept live active connections Skills: Understand BLE jamming and hijacking, know how to use BtleJack. 11. Web Bluetooth a) Introduction, security design consideration, sample implementations, possible attacks b) Interact with your BLE device via browser - run sample Web Bluetooth javascript code. Skills: Understand how to interact with BLE devices using javascript and risks involved. 12. BLE device firmware over the air update security a) Introduction, how the firmware update works, memory layout of BLE SoC b) Abuse insecure Over The Air firmware update in practice on provided Nordic Semiconductor SoC - Create zip image to flash (calculate CRC, no signing needed) - Update the firmware of device using nRF Connect mobile application - vulnerabilities depending on nRF SDK version c) Insecure OTA firmware upgrade in Texas Instruments SoC (taking control over wireless routers, stealing Tesla keys, ...) Skills: Understand security vulnerabilities of firmware update process in most popular SoCs. 13. Bluetooth 5, Bluetooth Mesh - theory introduction, hardware, new features and PHY, sniffing, beating new channel hopping RNG, possible attacks, … 14. Other attacks on BLE devices d) Attacking BLE devices via RF side-channel analysis (e.g. leaking AES key). e) Vulnerabilities in BLE SDK (e.g. RCE in Nordic SoftDevice) f) SoC vulnerabilities (memory readout protection bypass, fault injection,…). Sample attack to try out in practice on provided nRF51 development board 15. Brief review of the multitude attacks on BLE protocol and its implementations as well as attack tools (Bleedingbit, Sweyntooth, BlueFrag, KNOB, BIAS, BLESA, BLURTooth, Frankenstein, JackBNimBLE, …) 16. Summary, best practices, references, “hackme” challenges…
